Home > On-Demand Archives > Theatre Talks >
High Security RTOS
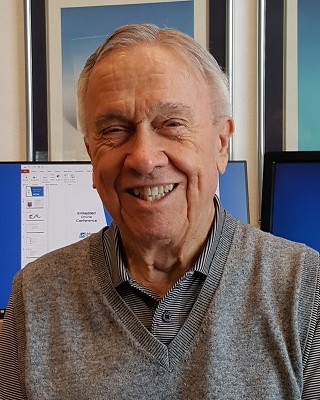
Ralph Moore - Micro Digital, Inc. - Watch Now - EOC 2024 - Duration: 39:49
This talk explores the features that can be added to an RTOS to create more secure microcontroller software. We start with the advantages of partitioning. Then show how to partition code and how to isolate the partitions. These methods build upon the security features of the Cortex-M architecture. Next, methods are introduced to limit system damage by malware that has invaded a partition. The talk includes numerous diagrams and code samples and emphasis is upon practical solutions that work. The presentation is expected to be beneficial to both programmers and security experts -- it introduces many new concepts that go beyond best programming practices. The talk concludes with suggestions for microcontroller security improvements to further advance the state of the art.
Hi Hammarbytp The things you mention are in addition to the RTOS, itself. HRoT is needed for secure boot and update, Encryption is needed for secure data transfer and secure update, etc. SecureSMX provides runtime protection against invasive actions by hackers. It protects against zero-days, unpatched vulnerabilities, and insider attacks. As such, it is another tool in the security toolbox.
very iinterested approach with security partitions and portals. if applied in restricted and regulated environment, is it backed by some security standards for easier certifications?
Hi cijart
Unfortunately, no. Currently, security standards and regulations are based upon the patch and update approach, even though it is not the only way to improve device security. We hope to change this. I think the standards and regulations need to be broadened in order to give OEMs more choices on how to meet security requirements.











Interesting, but I don't see it really meeting high security requirements without things like high integrity comms support, root of trust etc.
However it would make an excellent high integrity OS for safety applications (with some overlap for security)